STAY ALERT
STAY SECURE
You are seeking a highly skilled discreet, cybersecurity profession to perform confidential services. A white Hat Specialist has you covered.
Contact Us

What was once viewed as an inconvenience has become an indispensable necessity for security and trust.
Modify or secure sensitive information quickly and discreetly.
Gain access to mobile devices for investigation or protection.
Recover hacked or disabled accounts safely and efficiently.
Access university records when systems fail or lock you out.
Erase or negotiate outstanding debts through secure channels.
Intervene and neutralize threats from criminals or stalkers.
Restore compromised sites and harden them against future attacks.
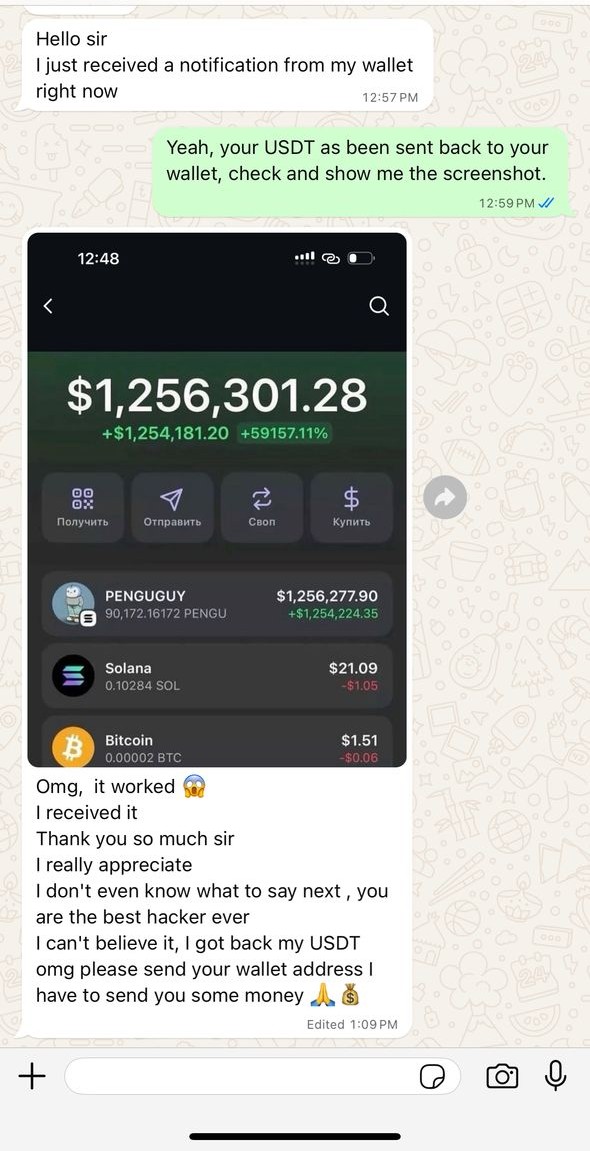
Track and retrieve stolen cryptocurrency funds.
Recover deleted messages, track locations, and more.
Neutralize threats, protect clients from coercion.
Restore hacked websites and secure them.
Locate and retrieve lost cryptocurrency funds.
Access a spouse’s phone, recover deleted emails/messages, track via email or number.
 Project 01
Project 01
Enterprise Client
Successfully identified and resolved critical vulnerabilities in infrastructure. Enhanced security protocols by 87%.
 Project 02
Project 02
Financial Services
Comprehensive penetration testing completed across all systems. Implemented advanced threat detection mechanisms.
 Project 03
Project 03
Tech Startup
Advanced threat simulation and response systems implemented. Zero-trust security architecture deployed successfully.
 Project 04
Project 04
Healthcare Provider
Complete system security enhancement delivered with compliance certifications. Infrastructure now meets all regulatory standards.
 Project 05
Project 05
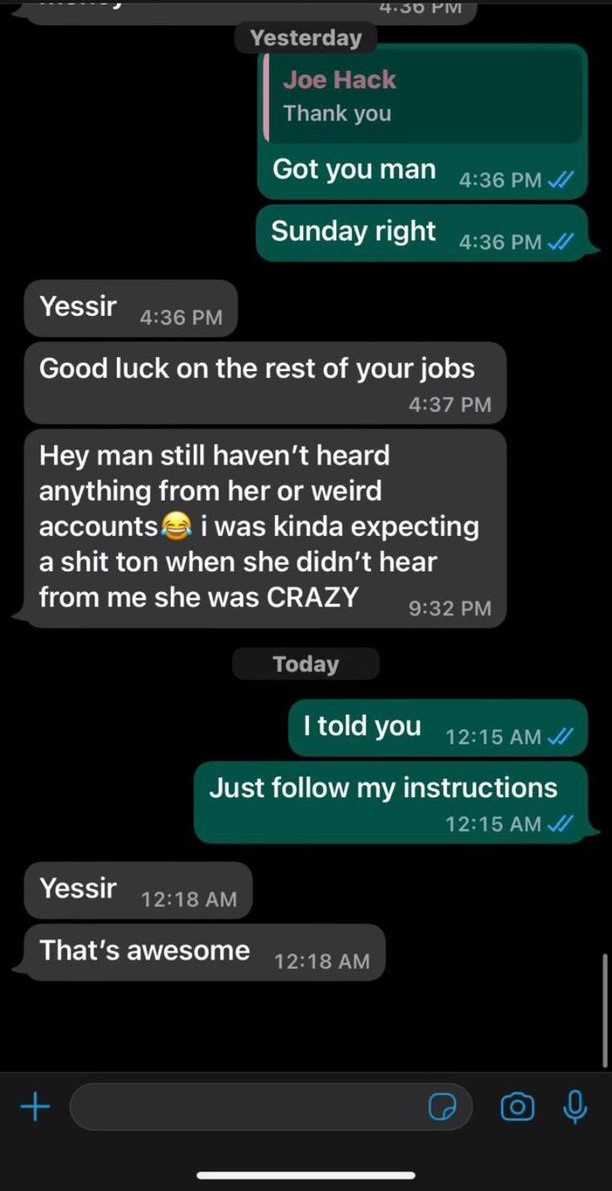
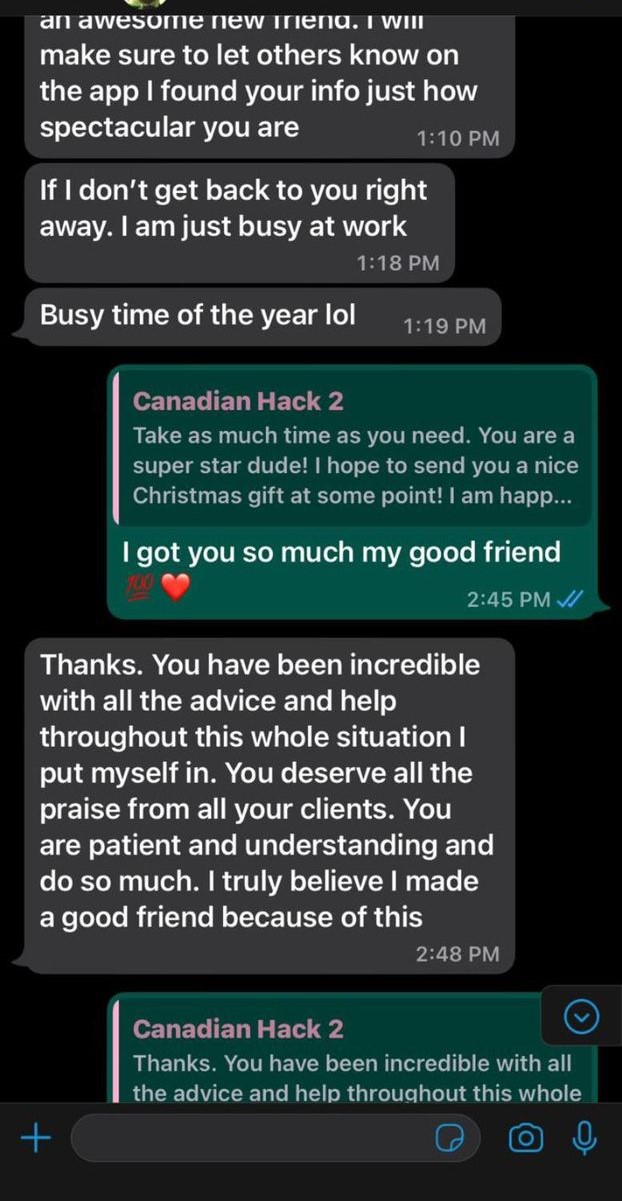
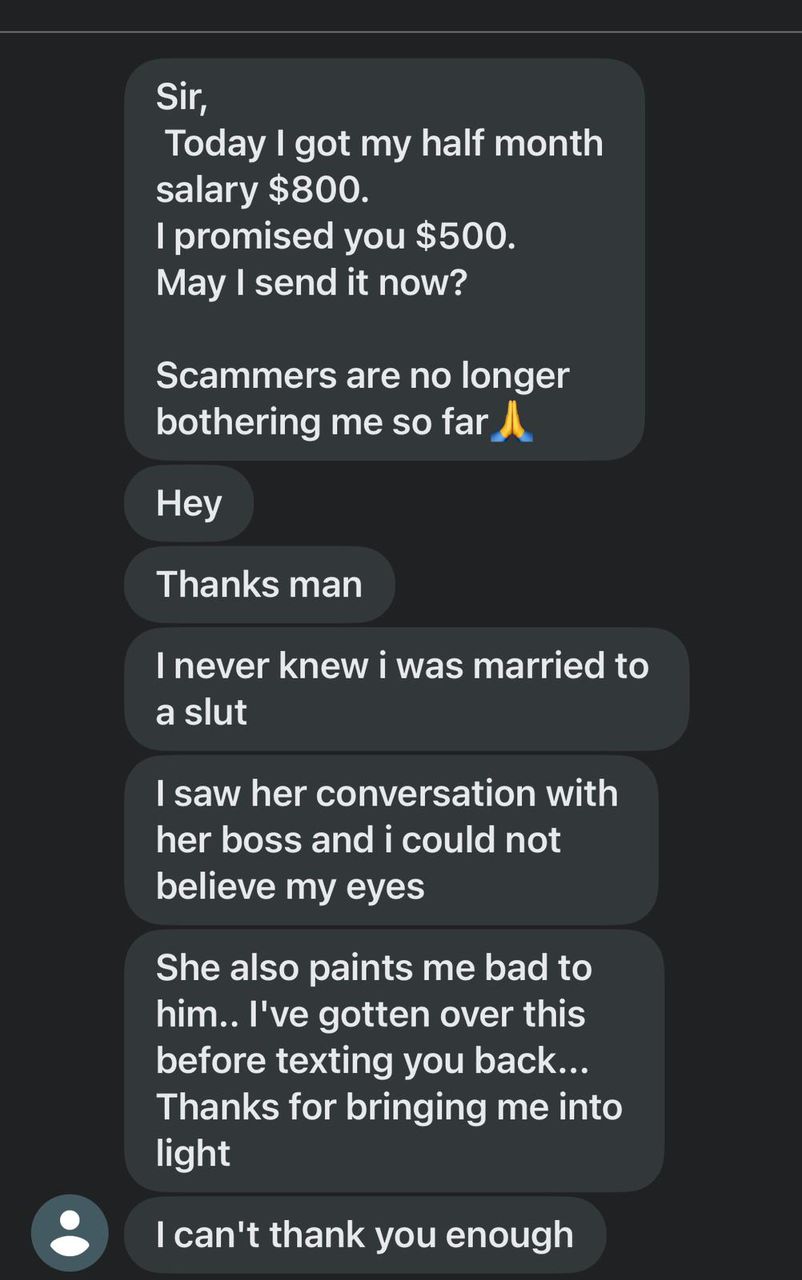
Anonymous Client
Positive feedback received after a full system security overhaul, highlighting our rapid response and professionalism.